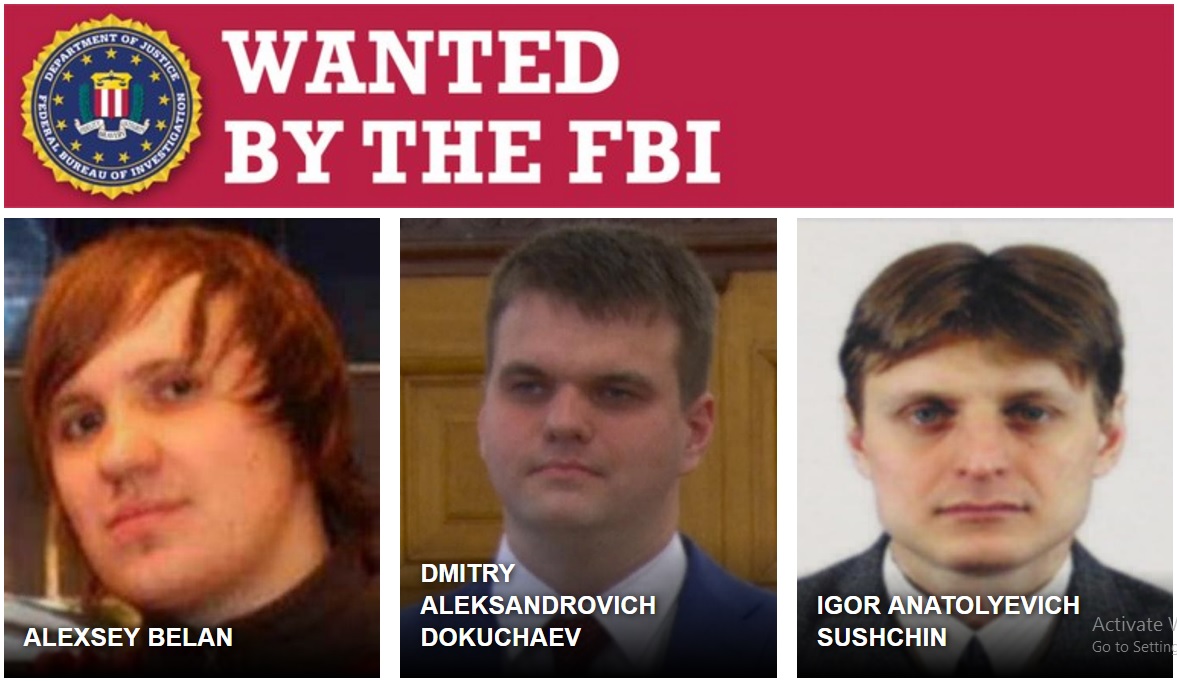
Cei patru inculpaţi sunt agenţii FSB Dmitri Dokuceaiev şi Igor Suşciin şi hackerii Aleksei Belan şi Karim Baratov, informează presa rusă.
Interesant e faptul ca unul dintre agenţii FSB inculpaţi în Statele Unite pentru atacurile cibernetice care au vizat compania Yahoo este arestat în Rusia pentru presupusa colaborare cu Agenţia Centrală de Informaţii din SUA (CIA), afirmă surse citate de presa rusă.
Potrivit agenţiei Sputnik, Dokuceaiev este unul dintre agenţii FSB acuzaţi de trădare şi arestaţi de autorităţile ruse în decembrie 2016. Ceilalţi suspecţi arestaţi în decebrie 2016 sunt Serghei Mihailov, agent FSB, şi un director al companiei Kaspersky Lab, Ruslan Stoianov.
Statele Unite nu au luat legătura cu Rusia pentru clarificări despre acuzaţiile în cazul atacurilor cibernetice care au vizat compania Yahoo, afirmă un oficial rus de rang înalt citat de agenţiile de ştiri Tass şi Sputnik. De altfel, presa oficială rusă susţine că ancheta în cazul atacurilor asupra Yahoo reprezintă o problemă politică internă a SUA.
Este prima dată când angajaţi guvernamentali ruşi sunt acuzaţi în Statele Unite pentru fraude cibernetice. Acuzaţiile se referă la atacuri informatice, fraude electronice, furt de secrete comerciale şi spionaj economic. Conform surselor citate, acuzaţiile vizează un atac cibernetic din 2014, în urma căruia au fost sustrase datele a 500 de milioane de utilizatori Yahoo. În septembrie 2016, compania americană a semnalat că hackeri angajaţi probabil de state au sustras, în urma unor atacuri cibernetice lansate în anul 2014, datele a cel puţin 500 de milioane de utilizatori de conturi online Yahoo. În decembrie 2016, compania a dezvăluit un alt atac, în urma căruia au fost sustrase datele a aproximativ un miliard de utilizatori de conturi online Yahoo. Acest atac cibernetic a fost comis în august 2013, dar a fost depistat abia în 2016, după ce servicii de securitate americane au furnizat companiei Yahoo date furate de o terţă parte. Hackerii au reuşit să sustragă nume de utilizatori, adrese de email, numere de telefon, date de naştere, dar şi parole de acces şi răspunsuri la întrebări de securitate, a transmis Yahoo, care susţine că nu au fost sustrase informaţii despre conturi bancare.
Potrivit publicaţiei Gazeta.ru, Dokuceaiev şi Mihailov ar fi colaborat cu CIA, dar această acuzaţie nu figurează în documentele oficiale ale anchetatorilor ruşi. Însă acuzaţiile ruse se referă la colaborarea cu servicii secrete străine.
Cotidianul The Washington Post a explicat că ancheta din SUA în cazul Yahoo nu are legătură cu investigaţia în cazul atacurilor cibernetice care au vizat serverele Partidului Democrat din SUA.
Cel puţin doi angajaţi ai Serviciului Federal de Securitate (FSB) din Rusia arestaţi în ancheta legată de atacurile cibernetice sunt acuzaţi de colaborare cu Agenţia Centrală de Informaţii din SUA, au declarat în ianuarie surse citate de agenţia Interfax. Doi ofiţeri ruşi de informaţii şi un expert în securitatea cibernetică au fost arestaţi sub acuzaţia de trădare pentru că ar fi oferit date serviciilor secrete americane, inclusiv despre atacurile informatice din timpul campaniei prezidenţiale din SUA.
“Serghei Mihailov, director al unui departament al Centrului FSB pentru Siguranţa Informatică, şi adjunctul său, Dmitri Dokuceaiev, sunt acuzaţi de trădarea jurămintelor prin colaborarea cu CIA”, a declarat un oficial din cadrul echipei de investigare. Ancheta vizează încă cel puţin şase persoane, inclusiv Ruslan Stoianov, un expert care lucra pentru compania de securitate cibernetică Kaspersky Lab, scriu publicaţiile La Stampa şi The Guardian. Detaliile anchetei sunt neclare şi intervin într-un moment delicat pentru noul preşedinte al SUA, Donald Trump, care a admis cu greu implicarea Rusiei în scrutinul prezidenţial american.
Statele Unite au anunţat, pe 29 decembrie, expulzarea a 35 de diplomaţi ruşi, închiderea a două misiuni diplomatice ruse, precum şi sancţiuni vizând oficiali şi entităţi de pe teritoriul Rusiei, pe fondul tensiunilor dintre Washington şi Moscova după ingerinţele ruse în campania electorală americană.
Preşedintele Rusiei, Vladimir Putin, a ordonat campania de influenţare a rezultatului scrutinului prezidenţial din SUA în scopul facilitării victoriei lui Donald Trump şi în ambiţia de a submina sistemul liberal-democratic occidental, au concluzionat serviciile secrete americane.
În octombrie 2016, Administraţia Statelor Unite a formulat acuzaţii oficiale la adresa Rusiei privind o serie de atacuri cibernetice care au vizat servere ale Partidului Democrat în timpul campaniei electorale pentru alegerile prezidenţiale şi legislative. În ultimele luni, oficiali americani au semnalat că atacurile cibernetice au fost efectuate de hackeri susţinuţi de Administraţia de la Moscova, scopul posibil fiind de a perturba campania în care candidata democrată la funcţia de preşedinte, Hillary Clinton, s-a confruntat cu republicanul Donald Trump. “Avem motive să credem, date fiind scopul şi sensibilităţile acestor eforturi, că aceste activităţi puteau fi autorizate doar de oficiali de rangul cel mai înalt din Rusia”, a transmis Administraţia SUA. Preşedinţia Rusiei a calificat drept “absurde” acuzaţiile Statelor Unite.
Iata comunicatul FBI :
Charges Announced in Massive Cyber Intrusion Case
Two of the Perpetrators Believed to be Russian Intelligence Officers

ALEXSEY BELAN

DMITRY ALEKSANDROVICH DOKUCHAEV

IGOR ANATOLYEVICH SUSHCHIN
Russian criminal hacker Alexsey Belan and Russian FBS officers Dmitry Dokuchaev and Igor Sushchin have been indicted on computer hacking, economic espionage, and other criminal charges. Also charged was criminal hacker Karim Baratov.
Four individuals—two Russian Federal Security Service (FSB) officers and two criminal hackers—have been charged by a federal grand jury in the Northern District of California in connection with one of the largest cyber intrusions in U.S. history, which compromised the information of at least 500 million Yahoo accounts.
One of the criminal hackers was arrested yesterday by Canadian authorities. The two FSB officers and the second hacker, last known to have been in Russia, are currently fugitives wanted by the FBI.
The indictments were announced today by U.S. Department of Justice Acting Assistant Attorney General Mary McCord, FBI Executive Assistant Director Paul Abbate, and Northern District of California U.S. Attorney Brian Stretch during a press conference in Washington, D.C.
The FSB is an intelligence and law enforcement agency of the Russian Federation, and it’s believed that the two FSB officers work in an FSB unit that serves as the FBI’s point of contact in Moscow on cyber crime matters. According to McCord, “The involvement and direction of FSB officers with law enforcement responsibilities make this conduct that much more egregious—there are no free passes for foreign state-sponsored criminal behavior.”
According to the indictment, from about April 2014 up to at least December 2016, FSB officers Dmitry Dokuchaev and Igor Sushchin directed this cyber intrusion conspiracy—which involved malicious files and software tools being downloaded onto Yahoo’s network—that resulted in the compromise of that network and the theft of subscriber information from at least 500 million accounts. This stolen information was then used to obtain unauthorized access to the contents of accounts at Yahoo, Google, and other webmail providers.
The indictment says that Dokuchaev and Sushchin paid, directed, and protected two known criminal hackers who took part in the scheme—Alexsey Belan, a Russian national and resident, and Karim Baratov, born in Kazakhstan and a naturalized Canadian citizen and resident. Belan, who has been indicted twice in the U.S. in the past for cyber-related crimes, is currently on the FBI’s Cyber’s Most Wanted list and is the subject of a Red Notice for Interpol nations, which includes Russia.
“This is a highly complicated investigation of a very complex threat. It underscores the value of early, proactive engagement and cooperation between the private sector and the government.”
FBI Executive Assistant Director Paul Abbate
The information stolen from the 500 million user accounts came from Yahoo’s proprietary user data base, which contained information such as users’ names, recovery e-mail addresses, phone numbers, and certain information needed to manually create account authentication web browser cookies.
What were the alleged perpetrators after? In part, they used access to Yahoo’s networks to identify and access accounts of possible interest to the FSB, including those of Russian journalists, U.S. and Russian government officials, and employees of U.S., Russian, and other providers whose networks the conspirators sought to exploit. Additional victim accounts belonged to private sector employees of financial, transportation, and other types of companies.
However, the co-conspirators were not above using the information they stole for personal financial gain. For example, Belan allegedly searched Yahoo user communications for credit card and gift card account numbers. He also leveraged the contact lists obtained from at least 30 million Yahoo accounts to perpetrate his own spam scheme.

FBI Executive Assistant Director Paul Abbate, with DOJ’s Acting Assistant Attorney General Mary McCord looking on, answers questions during a March 15, 2017 press conference announcing the indictments of four individuals on charges relating to the 2014 intrusion into Yahoo’s network.
Computer intrusions, by their very nature, are international in scope, so they require an international effort to unmask the worldwide hacking networks responsible for them. And this case was no different. Abbate expressed the Bureau’s gratitude to our international partners for their assistance and support leading up to these criminal charges today—specifically mentioning the Royal Canadian Mounted Police, the Toronto Police Service, and the United Kingdom’s MI5.
Another important aspect of this case involved the victim companies—including Yahoo and Google—coming forward and working with law enforcement. This collaboration ultimately resulted in countering the malicious activities of state actors and bringing criminals to justice. It also illustrates that the FBI can successfully work these kinds of investigations with victim companies while respecting the various concerns and considerations businesses might have about the impact of going public.
“This is a highly complicated investigation of a very complex threat,” said Abbate. “It underscores the value of early, proactive engagement and cooperation between the private sector and the government.”
Among the FBI’s major investigative priorities are to protect the U.S. against foreign intelligence operations and espionage and to protect the U.S. against cyber-based attacks and high-technology crimes. This case involved both. And it doesn’t matter to us whether the perpetrators of such crimes are run-of-the-mill criminals or sophisticated foreign states and their agents. With the help of our partners here and/or abroad, we will identify those responsible and hold them accountable for their actions.